Background Reading
Observations to Record
- Since you already ran Word before as normal user, now run-as Admin
- Compare (ODB console listing & ProcessCreate attributes) the privileged-execution with the previous (normal) Word execution & note down all differences
- Now run Notepad & run as admin, use privileged Word data & compare both console listings & graph structures. Hint: focus on sequence NOT lineage.
YJ's Findings
Using WordPad since the VM does not have MS Word installed.
Normal vs Privileged execution of WordPad
NormalPrivilegedComparisonPrivileged execution of WordPad vs NotePad
Privileged execution of NotePadComparison of WordPad vs NotePadMissing Early Processes
Root Cause(s) Analysis for Missing Edges on YJ's Windows VMSysmon is not perfect. One of the challenges of using it is that it changes quite quickly. Sometimes to a point that we have missing data.
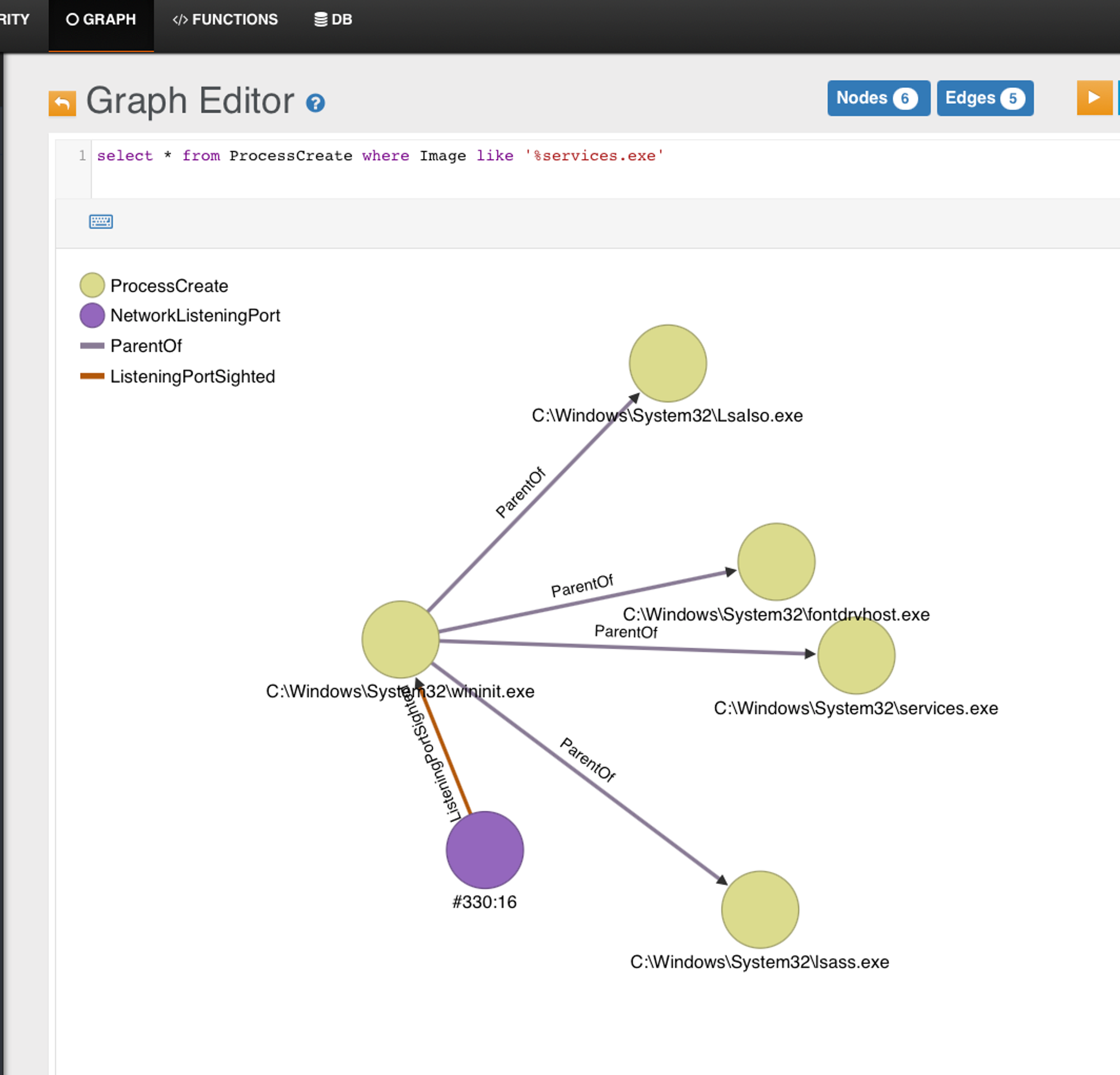
What started this section was due to YJ's environment somehow not capturing such a relationship like below:
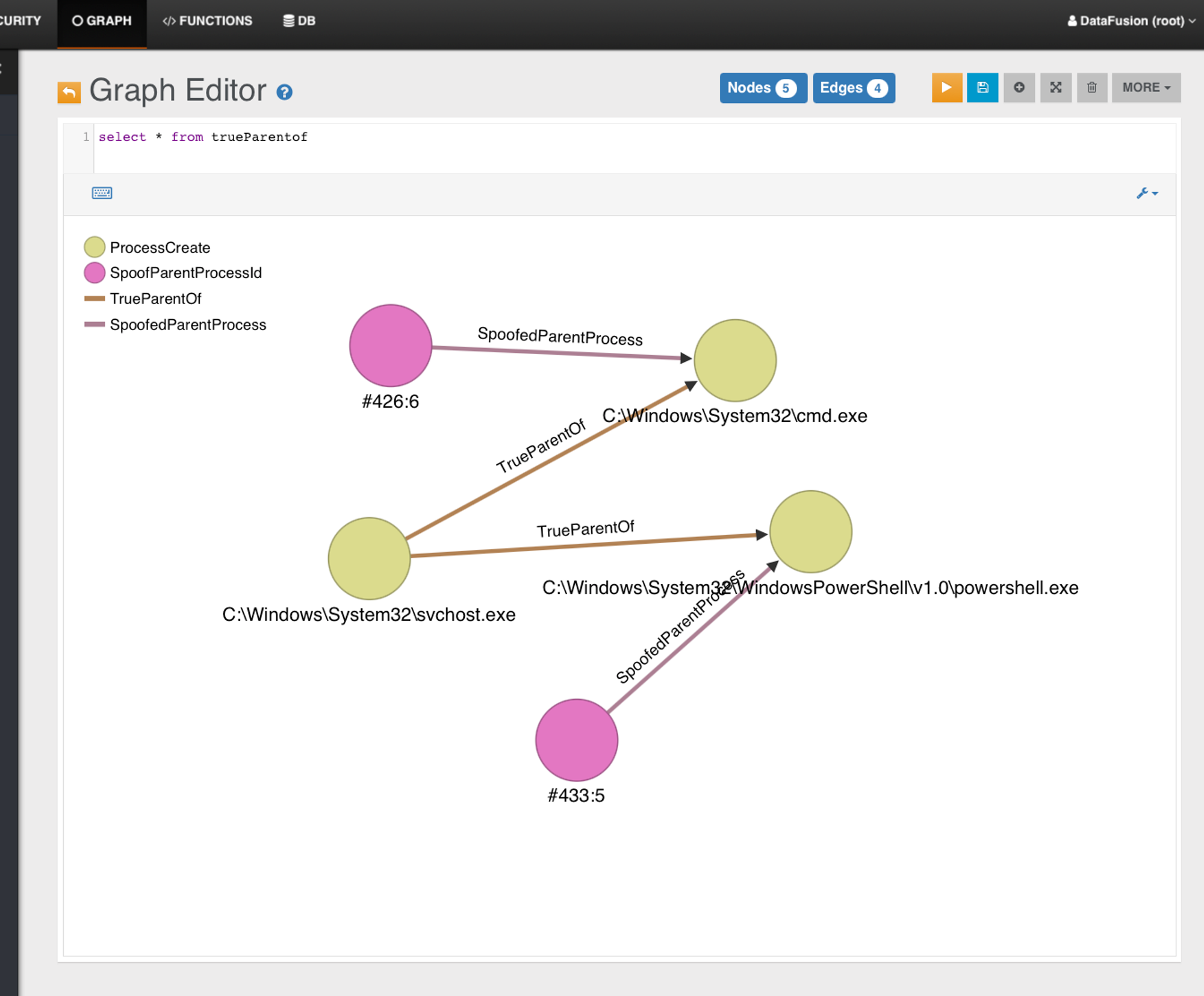
This backend graph is from a fresh cloud VPS backend instance. We can see that the true parent is an early process SVCHOST.exe which is in turn started by services.exe
After investigation on both physical Windows installations, Win10 Home & Enterprise. The Sysmon 10.42 used is simply not capturing early processes, which includes Services.exe. But in YJ's case it seems to be able to capture the TrueParent.. which should be a SVCHOST.exe if we are dealing with cmd or powershell UAC test-cases. Note that his case has NO ProcessGuid & the search is based on PID, which can be reused. But even so, we should be linking TrueParentOf edge.
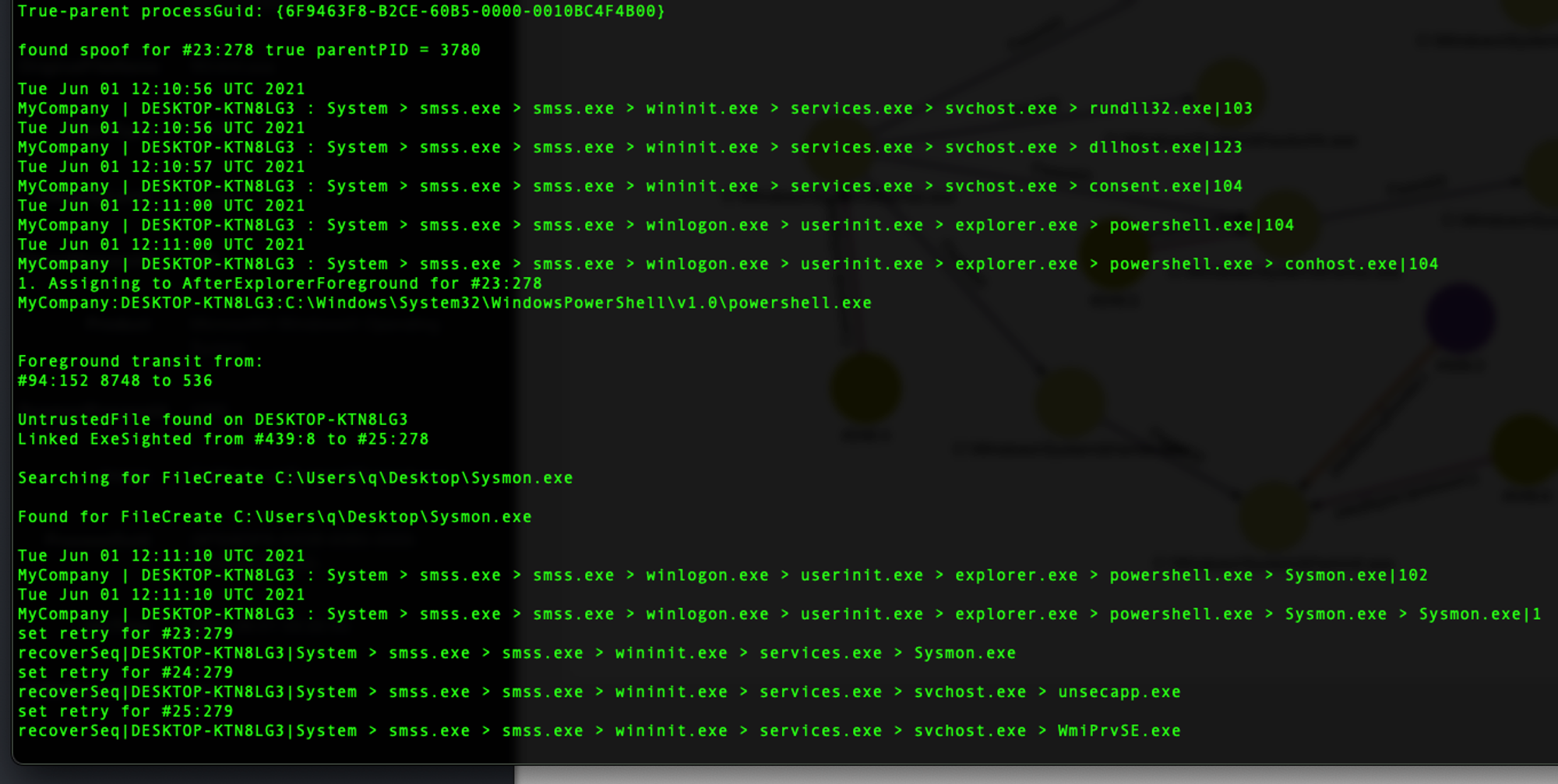
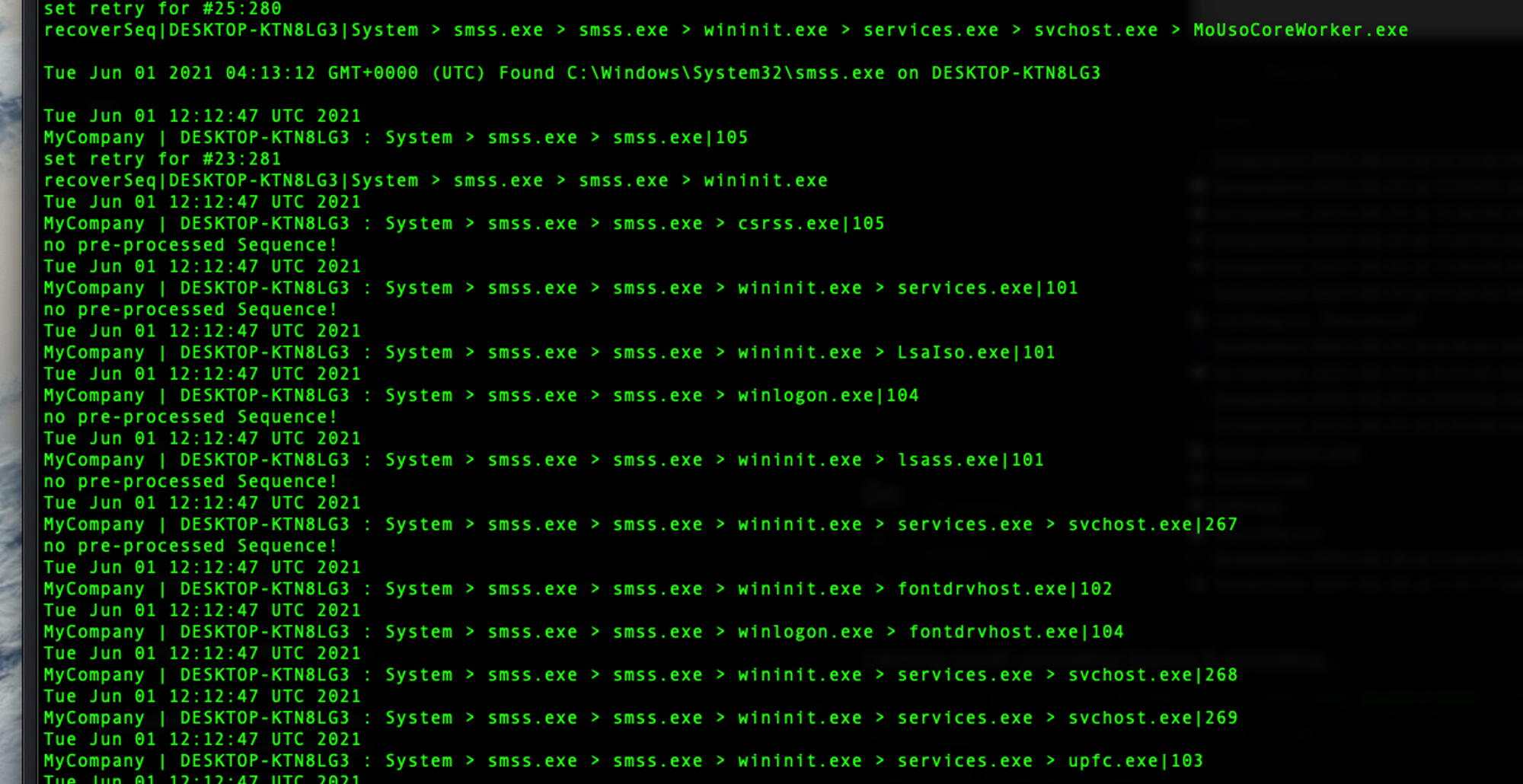
Even with the latest clean setup for both host agents & backend as shown below. We are missing quite a number of early processes wininit.exe for instance & so on. The symptoms we can see from ODB console is the recurrence of 'recoverseq|.....' output
Does it mean we are screwed?
- Depends on what kind of threats we are after. For early persistence, this weakness will hinder investigation
- For post-explorer type of infiltration cases, this is not really an issue.
Catching myself uninstalling Sysmon & reinstalling...
What about latest Sysmon (v13.20)
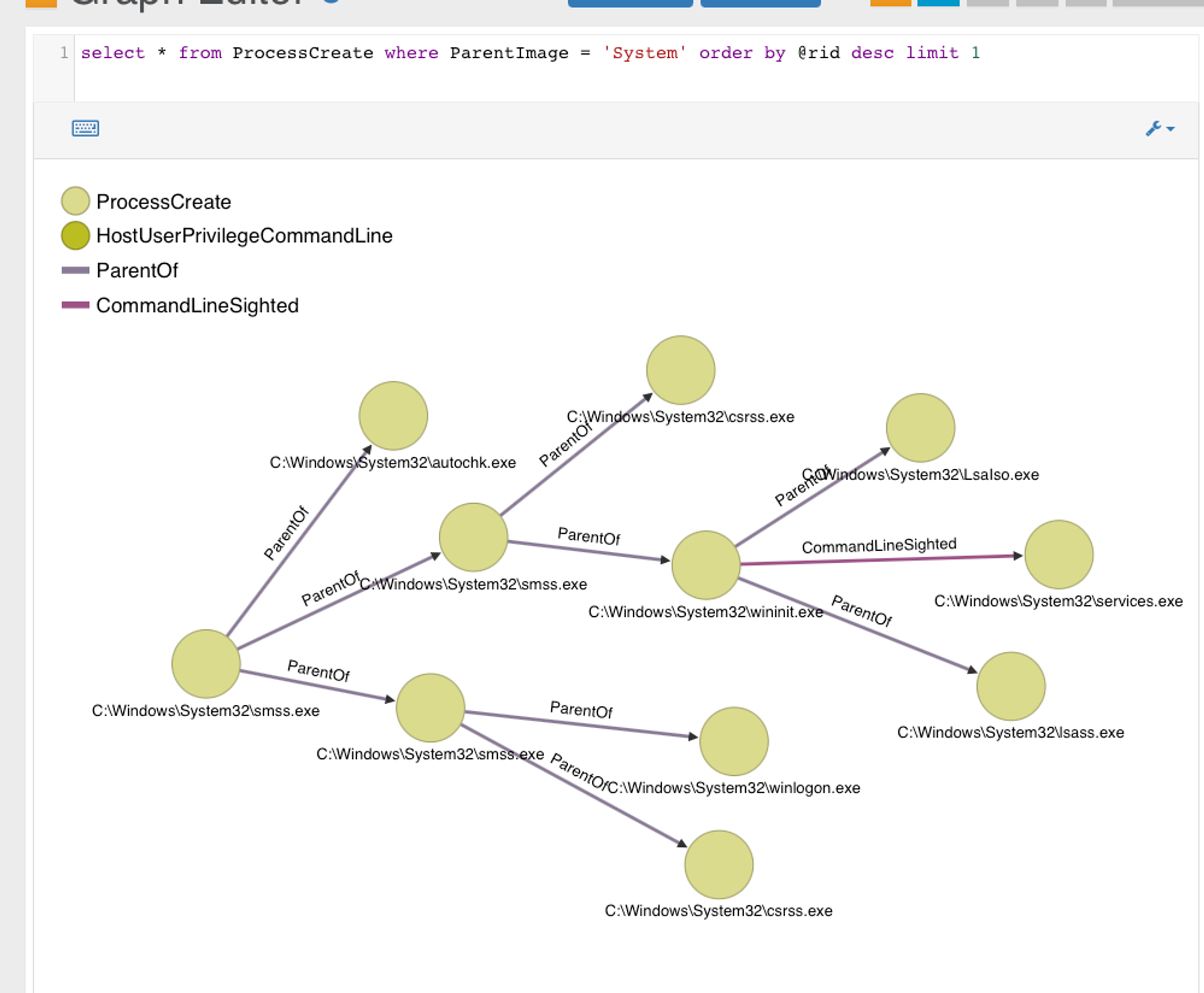
Better, at least we are capturing Services.exe & it seems the behaviour differs across Win10 versions. For Win10 Home, it's still as bad for the early processes. Following data-set are from Win10 enterprise.
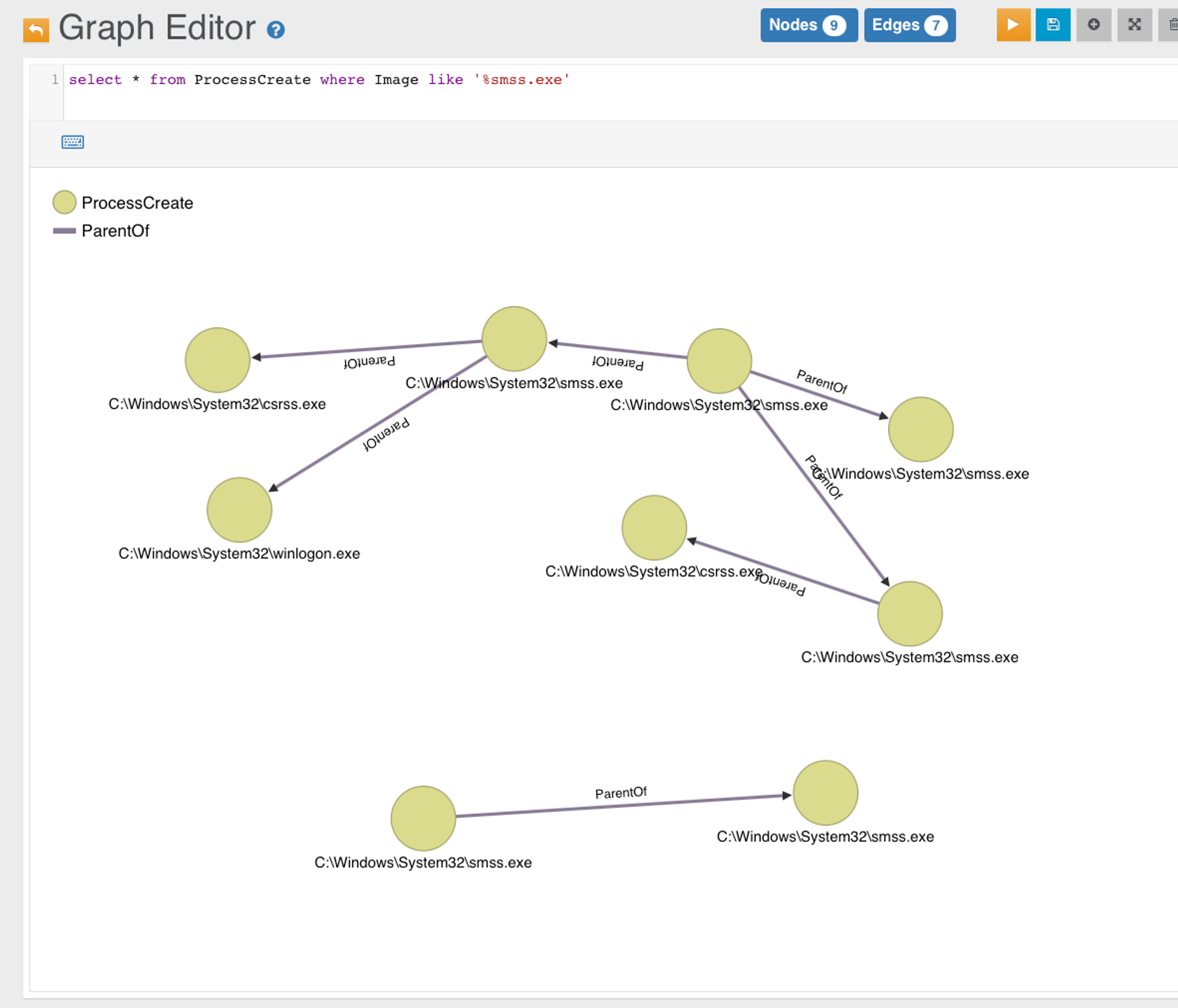
Parent (smss.exe) to Wininit.exe somehow not linked...
A more complete early processes lineage... services.exe in turn is parent to MANY SVCHOST.exe processes
So what's missing?
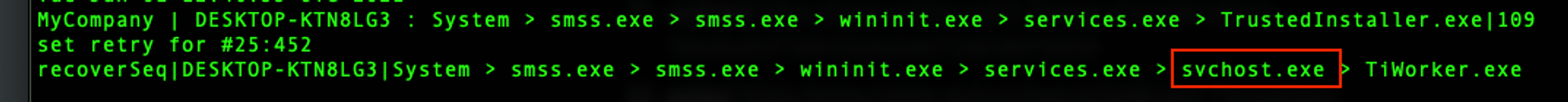
When we see a "retry", the backend is basically reconstructing or guessing the whole sequence based on the last pair, in the case below: svchost.exe > Tiworker.exe. This means svchost.exe is missing.