Related Goals
Use ODB console output for this
Background knowledge: https://github.com/jymcheong/OpenEDR/wiki/1.-Concepts-of-Operations#system-profiling-for-discerning-between-type-2-vs-3
Observations from ODB console output:
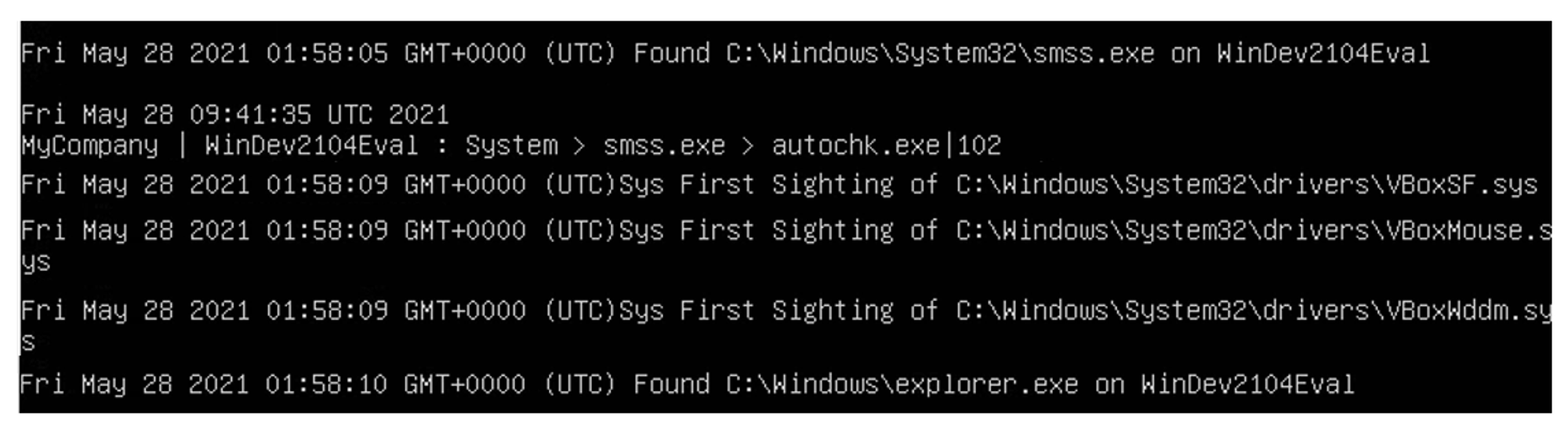
Upon booting up the Windows VM, the first line in ODB console was about the finding of smss.exe. smss.exe (Session Manager Subsystem) is responsible for creating the user-mode environment that provides the visible interface to Windows. It is an important component of the Windows OS that starts running immediately when the machine is booted up.
After smss.exe was found, we see that autochk.exe was created by smss.exe. autochk.exe runs when the computer is started to verify the logical integrity of the file system.
The subsequent 3 lines in ODB console were about the sighting of VirtualBox drivers, which will be loaded up by VirtualBox during bootup. After the sighting of VirtualBox drivers, explorer.exe was found on the machine. explorer.exe is part of Windows OS and provides a graphical user interface for accessing the file systems.
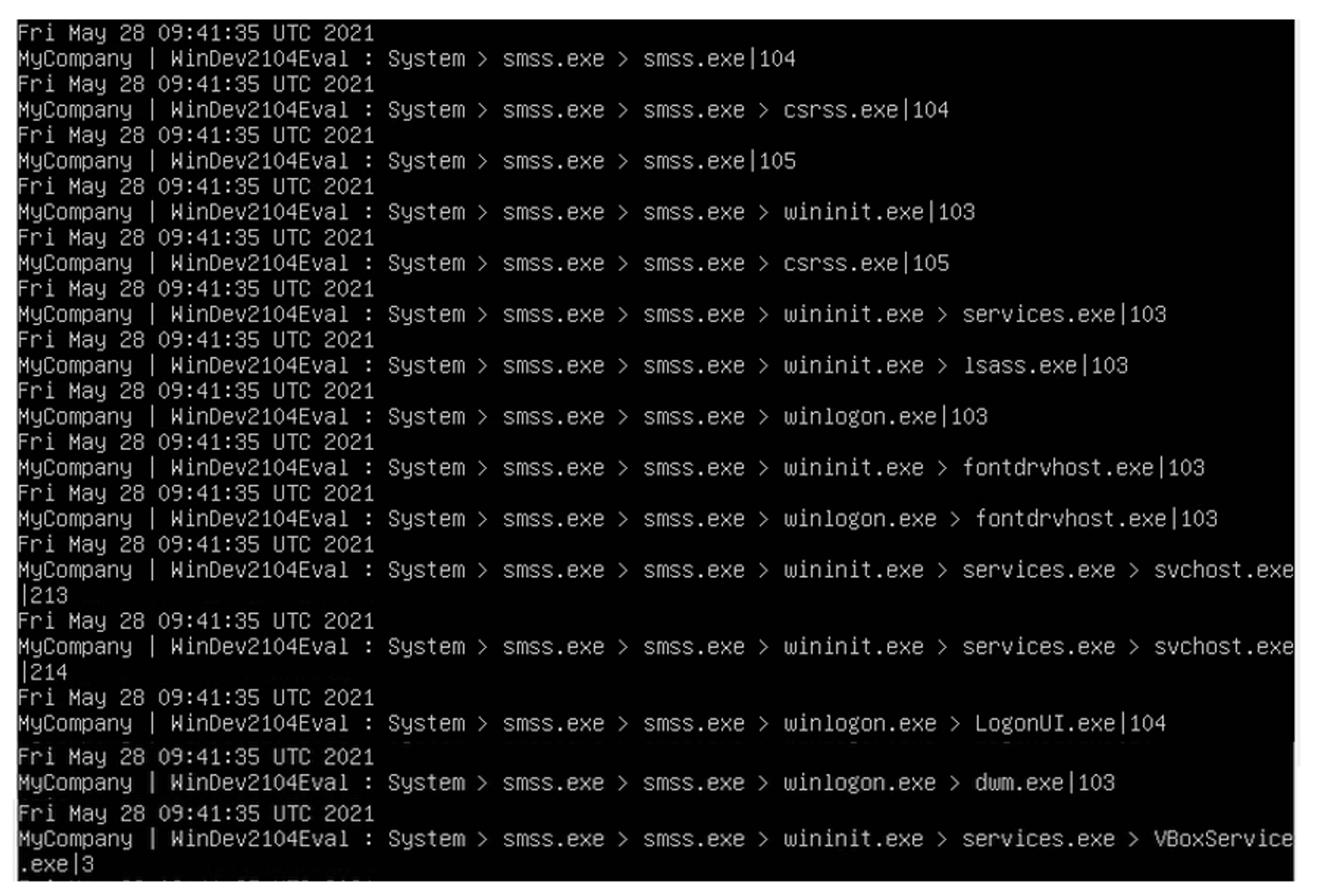
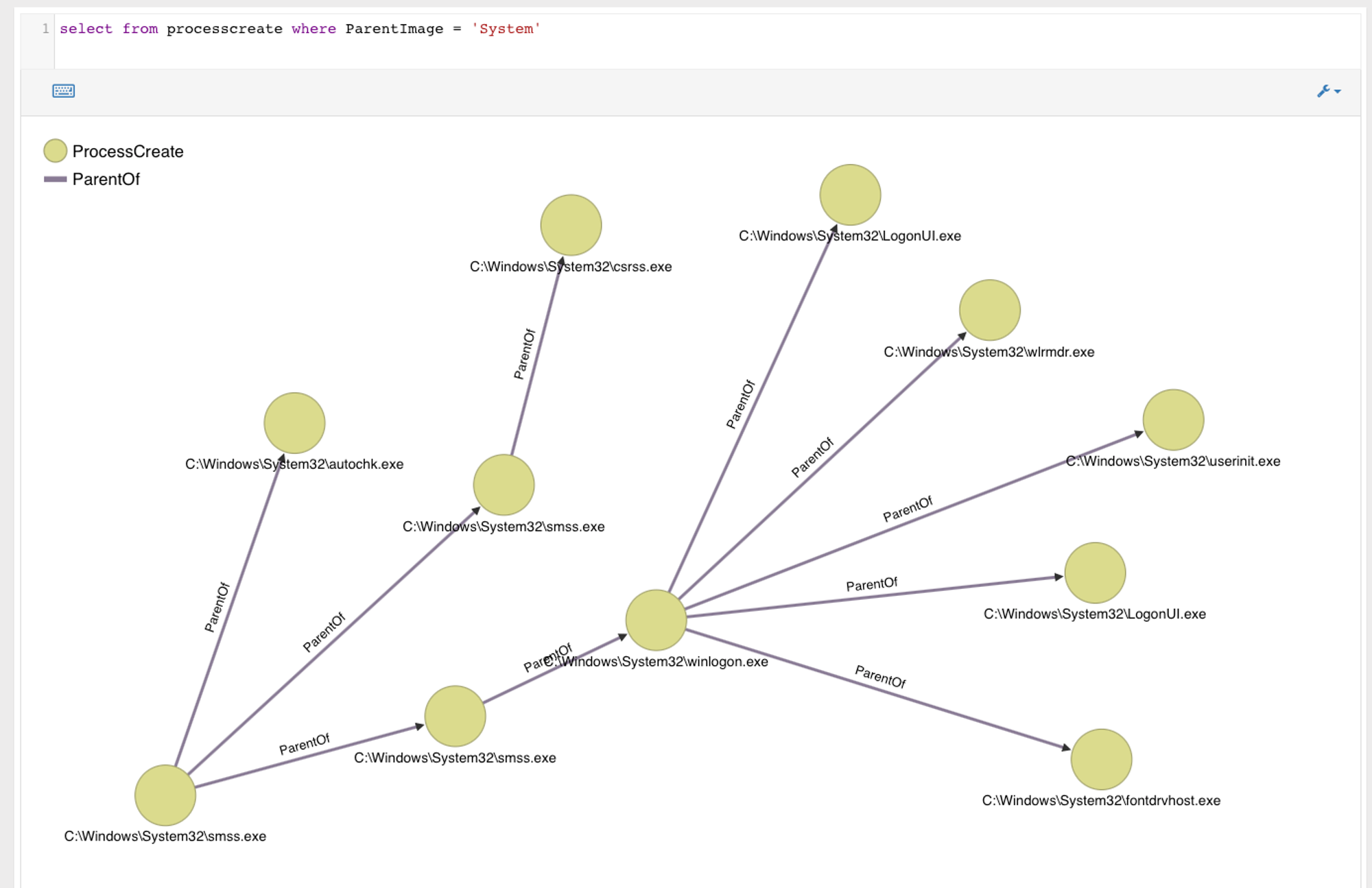
Summary of processes that were created during boot-up
Process Name
What is it/What does it do
Provides the user mode side of the Windows subsystem.
Responsible for running the Windows Initialization process.
Manages the operation of starting and stopping services. It also deals with the automatic starting of services during the computers boot-up.
Verifies the validity of user logons to the machine.
Responsible for handling the secure attention sequence & loading the user profile on logon
Manages the font drivers in the current user account
Shared service process that allows many Windows services to share a single process.
Responsible for the interface you see on the log on screen.
Responsible for your graphical user interface. In particular, it helps to generate visual effects, such as transparent windows and taskbar thumbnails.
Software installed on a VirtualBox guest to enhance performance and functionality. Runs on startup.
Importance of knowing normal bootup sequence
As seen from the findings above, Windows OS has processes that run automatically on system boot or account logon. It is important that we understand the normal bootup sequence to know what kind of processes are created during bootup. This is because attackers may configure system settings to automatically execute a program during system boot to maintain persistence on compromised systems. By knowing normal bootup sequence, we can then spot out unknown/unusual process creation during the bootup process.
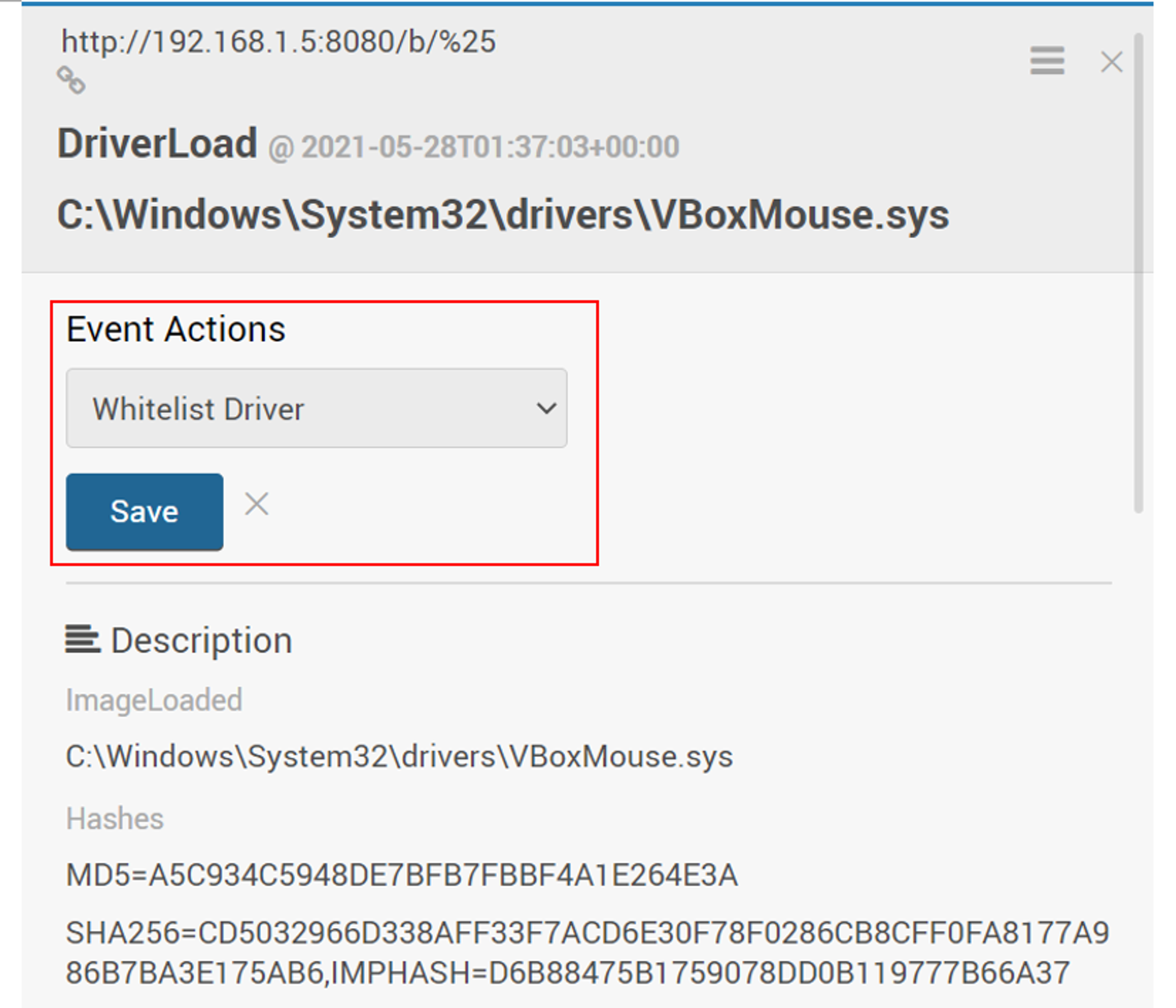
Whitelisting of VirtualBox drivers
As seen during the bootup process, 3 VirtualBox drivers were loaded. To verify the authenticity of drivers, we should check whether it is signed or unsigned. A signed driver means that the driver software is associated with a digital certificate that allows identification of the publisher of the driver. It also ensures that the driver has never been modified by anyone else, as that would corrupt the signed status and make it unsigned. To check the signature of the VirtualBox drivers:
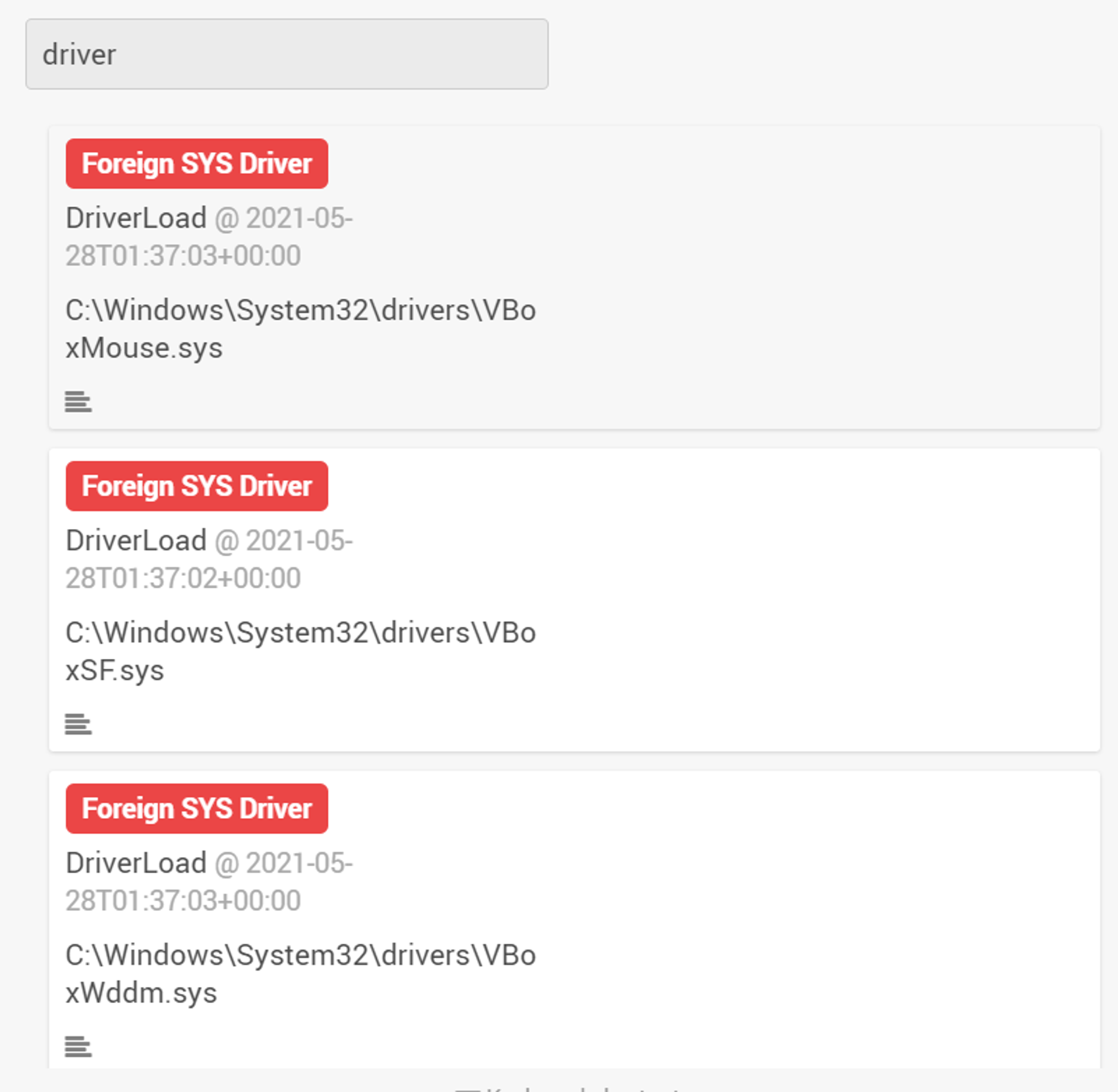
Step 1: Search for the drivers in Wekan
Step 2: Select the driver that you wish to investigate. Under Description, you will be able to see whether the driver is signed and by who.
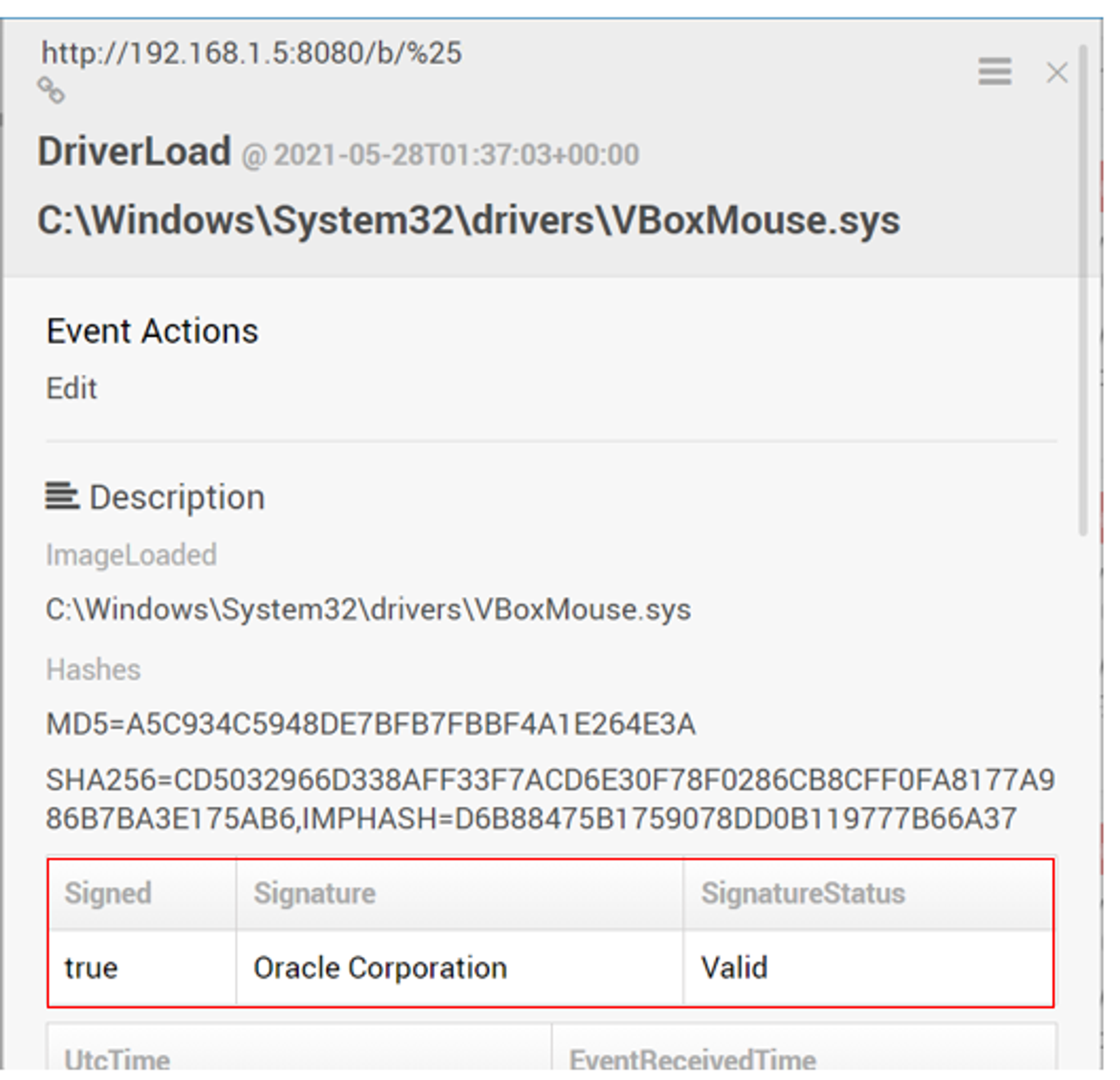
Step 3: In this case, since the driver is signed and has a valid signature status, we can whitelist the driver under Event Actions.