Some Samples
This track is a bit like catching Pokemon... I share some of mine:
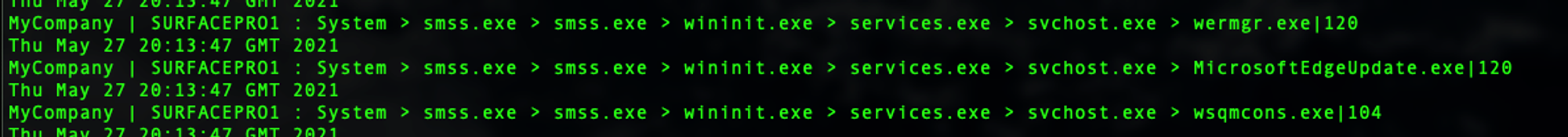
- Notice the lineage...
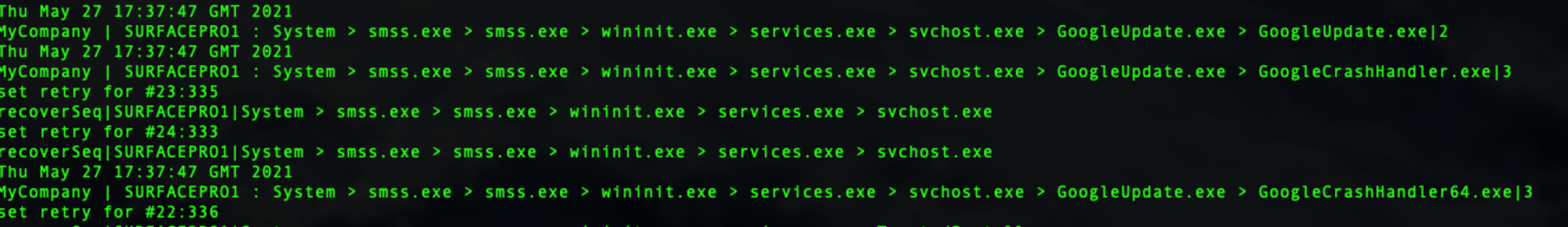
- Updates (Google) can crash too... for Windows modules, there's a WerFault.exe
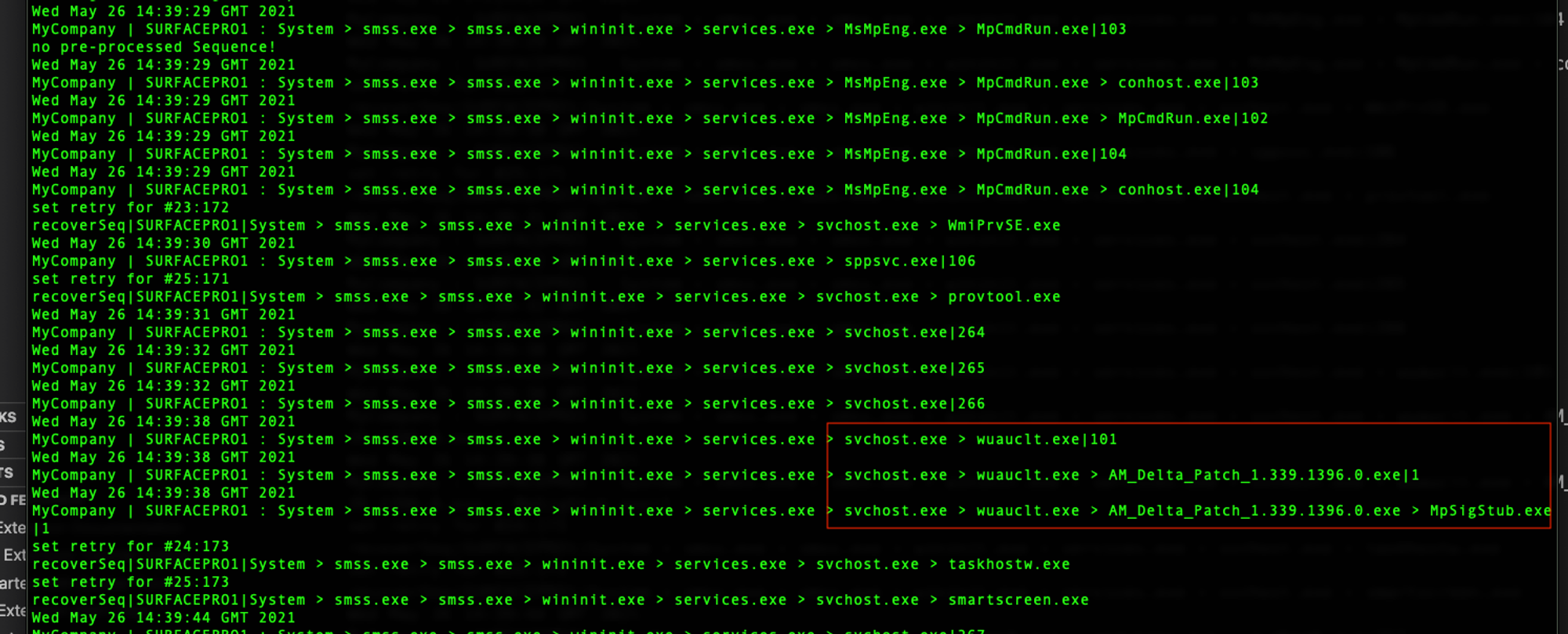
- Notice the file naming convention...
YJ's Observations
List of processes used for software updates
Name of Process
Purpose
Image Path
Sequence
To update Visual Studio
C:\Program Files (x86)\Microsoft Visual Studio\Installer\resources\app\ServiceHub\Services\Microsoft.VisualStudio.Setup.Service\VSIXConfigurationUpdater.exe
System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > VSIXConfigurationUpdater.exe
To update Microsoft Edge
C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe
System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > MicrosoftEdgeUpdate.exe
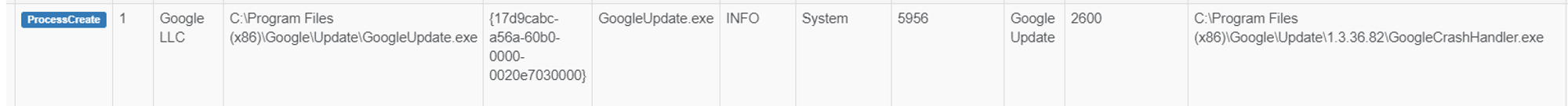
To update Google Chrome
"C:\Program Files (x86)\Google\Update\GoogleUpdate.exe" /c
System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > GoogleUpdate.exe > GoogleUpdate.exe
Part of the Windows Automatic Update tool whose role is to extract downloaded Windows Updates
C:\Windows\Temp\4756BEFE-AF47-438C-B789-26227AF49B43\MpSigStub.exe
System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > wuauclt.exe > updateplatform.exe > MpSigStub.exe
Windows Update AutoUpdate Client. It checks with the Microsoft website for updates to the operating system.
C:\Windows\System32\wuauclt.exe
System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > wuauclt.exe
To update OneDrive
C:\Users\User\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe
System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > OneDriveStandaloneUpdater.exe
One observation is that most software updates sequence starts with System > smss.exe > smss.exe > wininit.exe > services.exe > svchost.exe > ...
As mentioned above, software updates can crash e.g. GoogleUpdate.exe
Jym's Comments
Dealing with False-Positive arising from Software updates
So YJ made a good observation that Microsoft & even some Google updates are triggered or originated from a SVCHOST started by services.exe. The other thing to note about such software updates is the use of number versioning within the Image path, some apps may even use numbering in directory names.
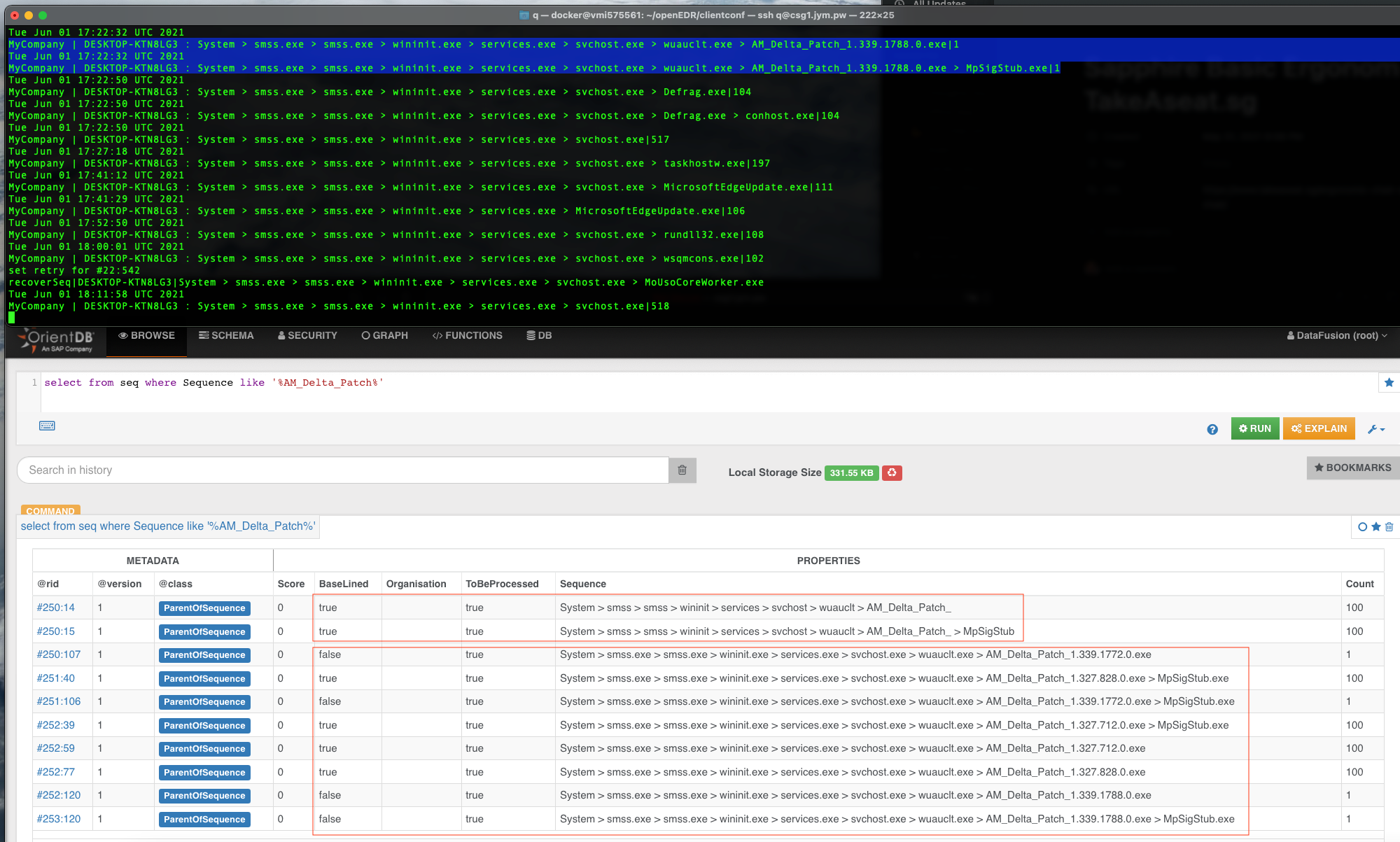
I want to take the opportunity to explain how OpenEDR whitelist such occurrences. When we whitelist AM_Delta_Patch_xxxxxxx (Microsoft Anti-malware updates), the backend function strips (a regex) numbers & dots away, in this case .exe, all numbering and dots ar removed to form the first red box sequences.
During detection phase, when the backend encounters a Sequence that has a (frequency) Count of 1, it does NOT immediately raise an alert, it will perform the exe, numbers & dots stripping & search against ParentOfSequence (seq is a short-hand) records again. If found, it treats the new sequence as OK, otherwise flag an alert.
