FileCreate
FileCreate events are logged when a file is created, overwritten or downloaded from the Internet. This event is useful for monitoring autostart locations, like the Startup folder, as well as temporary and download directories, which are common places malware drops during initial infection.
Example of FileCreate in Goal 7:
7. Perform IM platform use-case in Goal 1 and look at sequence generatedFileCreateStreamHash
FileCreateStreamHash events are logged when a named file stream is created i.e. download a file from the Internet, and it generates events that log the hash of the contents of the file to which the stream is assigned (the unnamed stream), as well as the contents of the named stream. There are malware variants that drop their executables or configuration settings via browser downloads, and this event is aimed at capturing that based on the browser attaching a Zone.Identifier “mark of the web” stream.
Reference: https://docs.microsoft.com/en-us/sysinternals/downloads/sysmon#event-id-15-filecreatestreamhash
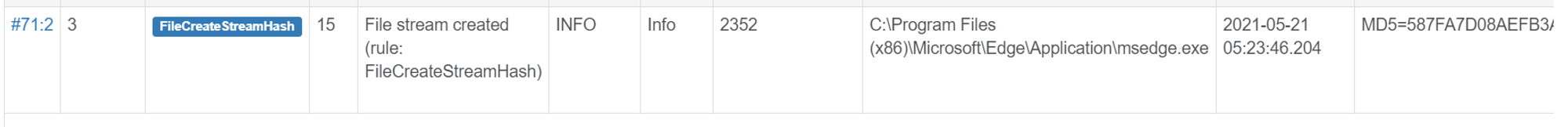
Example of FileCreateStreamHash when I downloaded the docx file from Web Gmail:
FileCreateTime
The event is logged when a file creation time is explicitly modified by a process. This event helps tracking the real creation time of a file. Attackers may change the file creation time of a backdoor to make it look like it was installed with the operating system. Note that many processes legitimately change the creation time of a file; it does not necessarily indicate malicious activity.
Examples of FileCreateTime events:
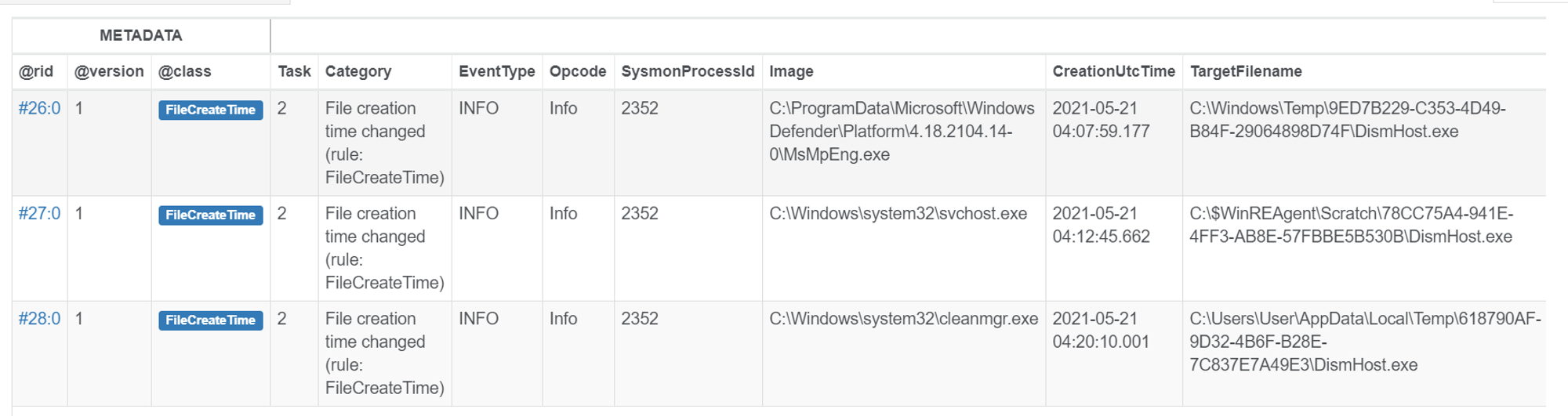
Seems that FileCreateTime events are generated during computer maintenance by processes like cleanmgr.exe (Disk CleanUp tool) and MsMpEng.exe (Part of Windows Defender).
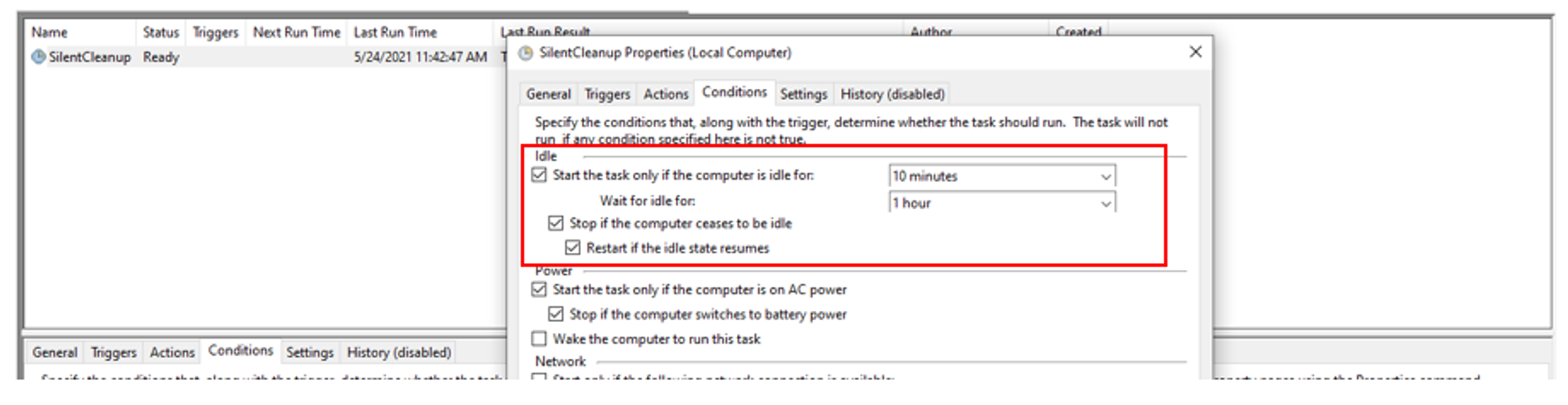
Looking into Task Scheduler, we can see that cleanmgr.exe is scheduled to run when the computer has been idle for 10 minutes & when the computer is on AC power. This explains why cleanmgr.exe was running even though I did not run the tool.
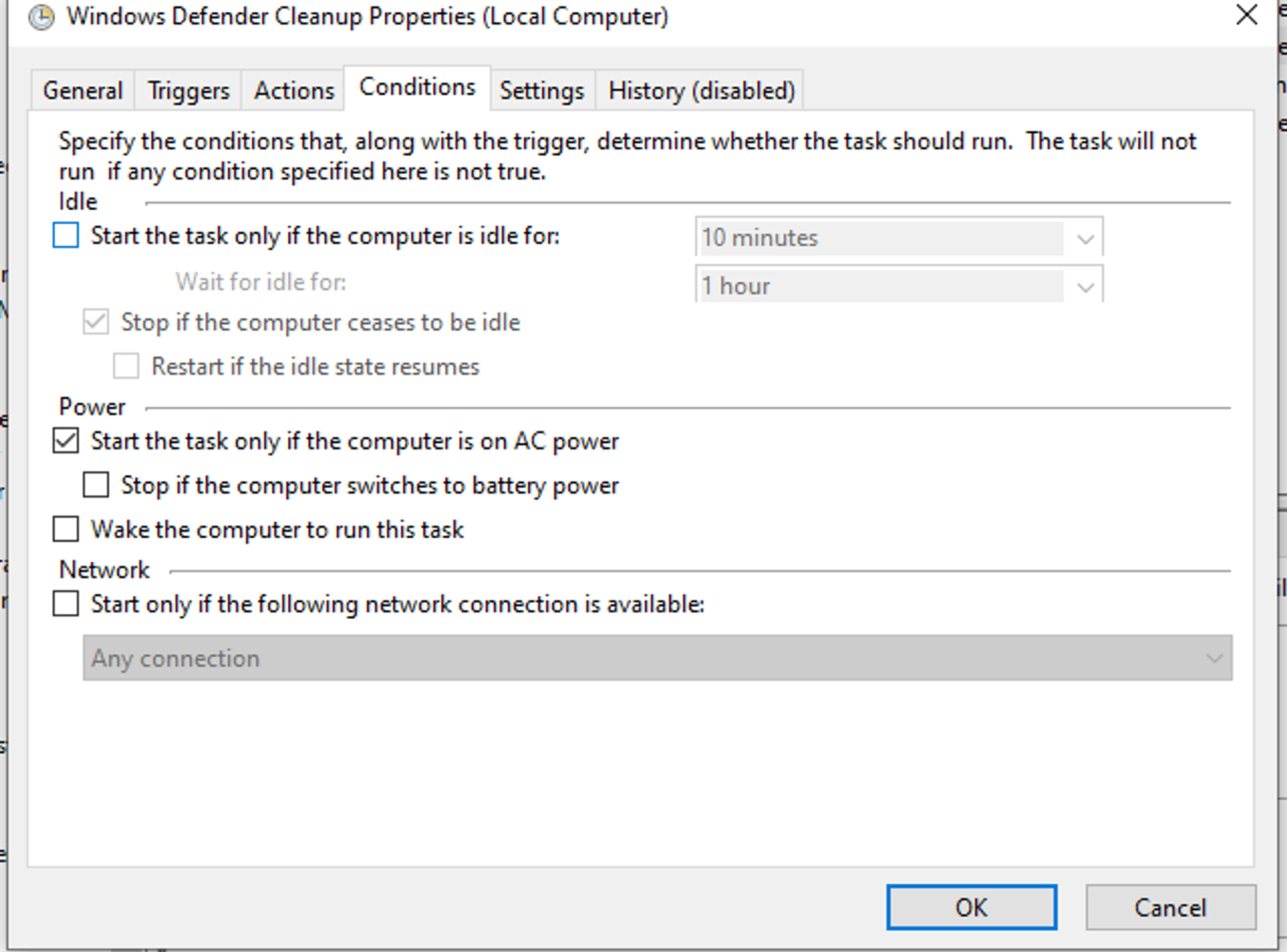
Similarly, Windows Defender has also been scheduled to run when the computer is idle and on AC power.