You can refer to https://www.notion.so/jymcheong/6-Install-Backdoor-3c893f16cdb241d0bd5a897429ac25e3#c3a6978d51504a2998a31a1b0e760454 where I manually ran the
exploit/windows/local/registry_persistence module to gain persistence and documented down my observations from OpenEDR.Since the module worked, I decided to choose this module to automate the process of establishing persistence on a victim's machine.
Issue Encountered
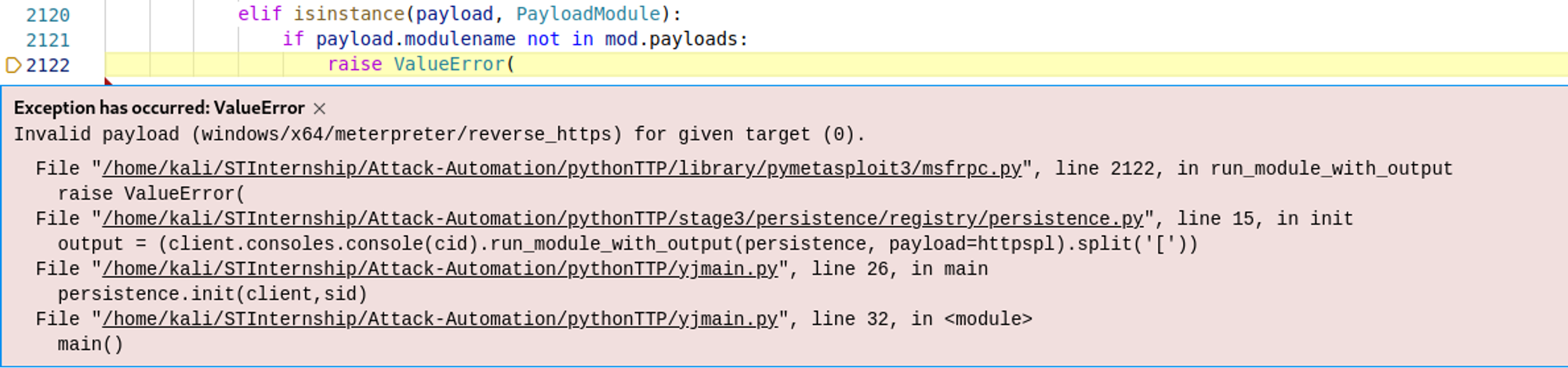
For some reason, I encountered an error stating that the payload is invalid even though it worked when done manually:
Solution:
After trial and error by testing with different payloads, I found out that the inclusion of x64 in the payload was causing the error. To resolve this error, I changed the payload from
windows/x64/meterpreter/reverse_https to windows/meterpreter/reverse_https.This showed a limitation of automation testing - what works when done manually might not work when done automated.
End Product
You can view my codes at https://github.com/real-yj98/Attack-Automation/blob/master/pythonTTP/stage3/persistence/registry/persistence.py.
If the module is successfully executed, it will print out
[+] Backdoor successfully installed! as shown below:
If the module failed to execute, it will print out
[+] Failed to install backdoor! instead.