AutoTTP
jymcheong • Updated Apr 12, 2022
What is TTP?
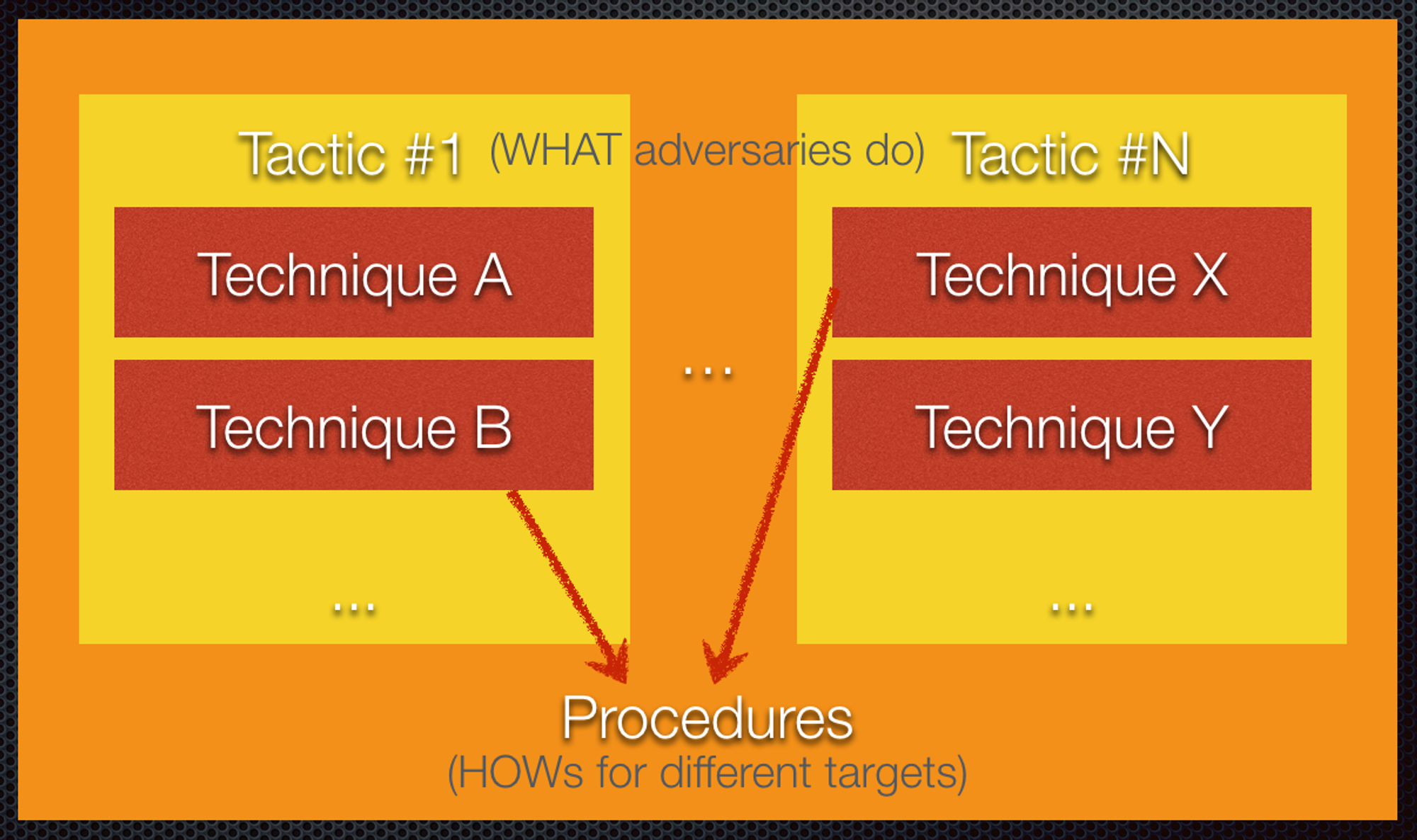
A tactic is the highest-level description of the behavior; techniques provide a more detailed description of the behavior in the context of a tactic; and procedures provide a lower-level, highly detailed description of the behavior in the context of a technique. The behavior of an actor. - NIST CSRC
Abstract definitions tend to lead to “so what?”, what is it that defenders need to understand?
- Tactics are sub-objectives (WHAT). When attacks are successful, there will be impacts to Confidentiality (e.g. attacker’s objective is to steal), Integrity (tamper) & Availability (deny) for Informational Systems. For Cyber-Physical systems, attacks can impact Safety with kinectic consequences (i.e. damage).
- Techniques are specific methods (HOW) to achieve various sub-objectives. Different systems require different techniques.
- Procedures are stringing techniques (WHEN to do WHAT, think OODA) together to achieve the desired offensive objectives.
Why Automate with AutoTTP?
- Tedious to manually re-run complex pen-testing procedures for regression tests, product evaluations, generate data for researchers & so on
- Modular & reusable
- Organise with whatever TTP mental-models you prefer
How?
- Pentesting-as-Code, goes hand-in-hand with Infra-as-Code to use in a Cyber-Range
- Any offensive tooling with API