What is Pushbullet?
Pushbullet is a service/application which allows you to share notifications and other text messages between your devices. They also provide an API, to allow users to send notifications from scripts or other programs. As Pushbullet app is currently not available in Linux, we will have to make use of the API in order to push notifications.
Setting up Pushbullet
Step 1: Create a Pushbullet account at https://www.pushbullet.com/
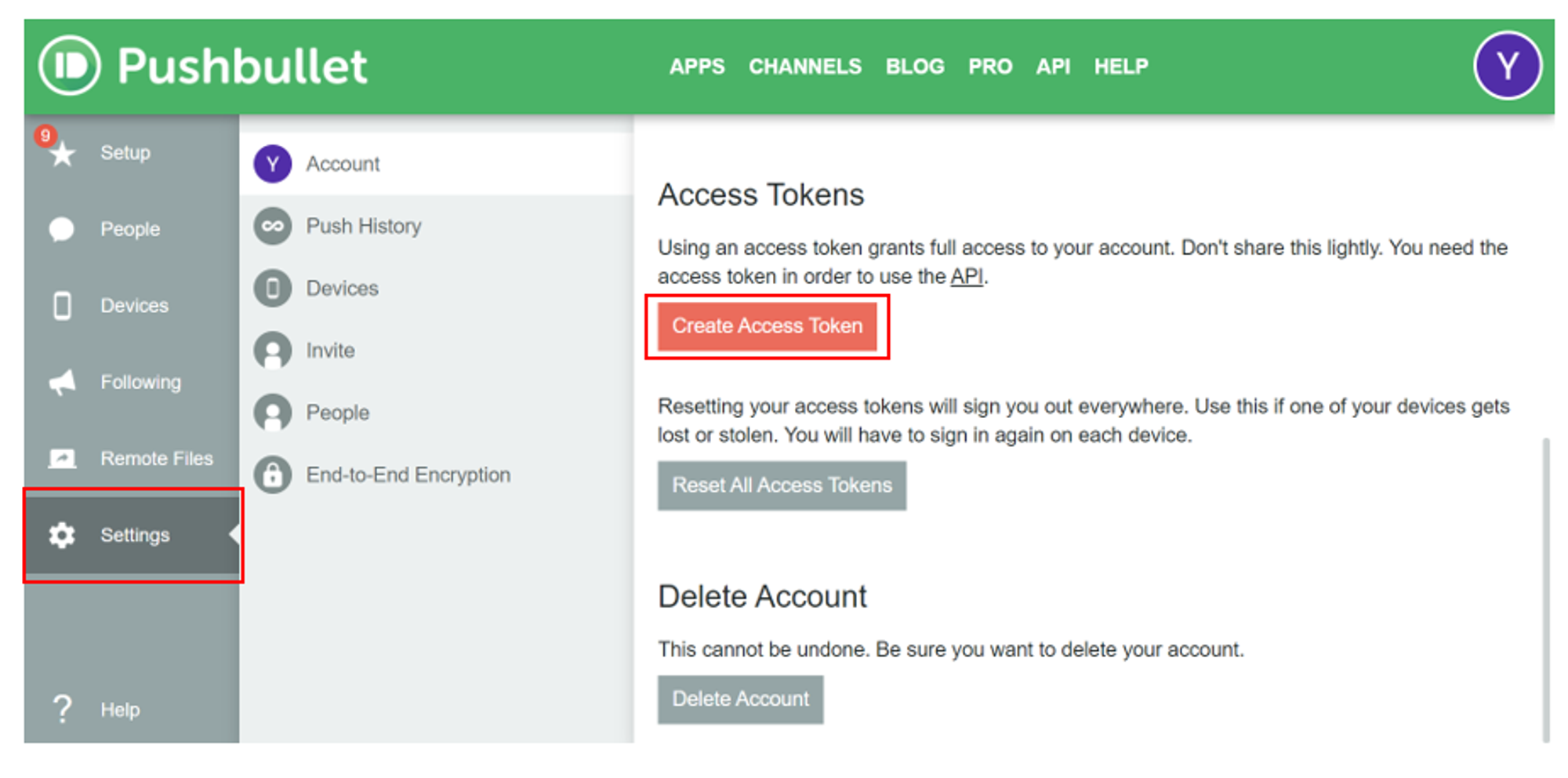
Step 2: After you have logged in, click on Settings and look for the ‘Access Tokens’ heading on the content section. Then, click on ‘Create Access Token’.
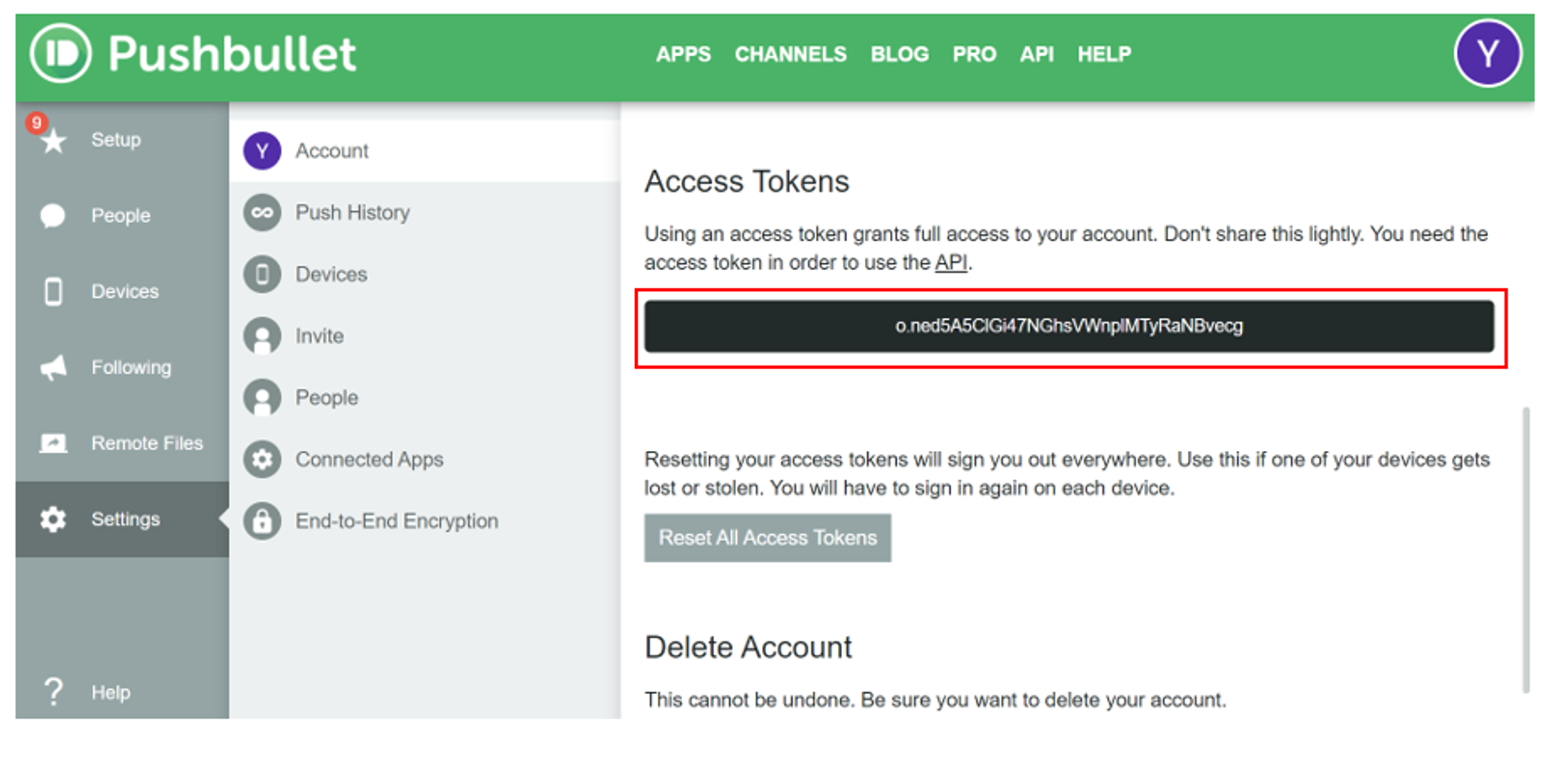
The token will then be created and shown on the screen. The purpose of this Access token is to act as an identification number for the Pushbullet account. We will use this Access Token to set up the script that sends push messages from our Linux VM.
Pushbullet Script
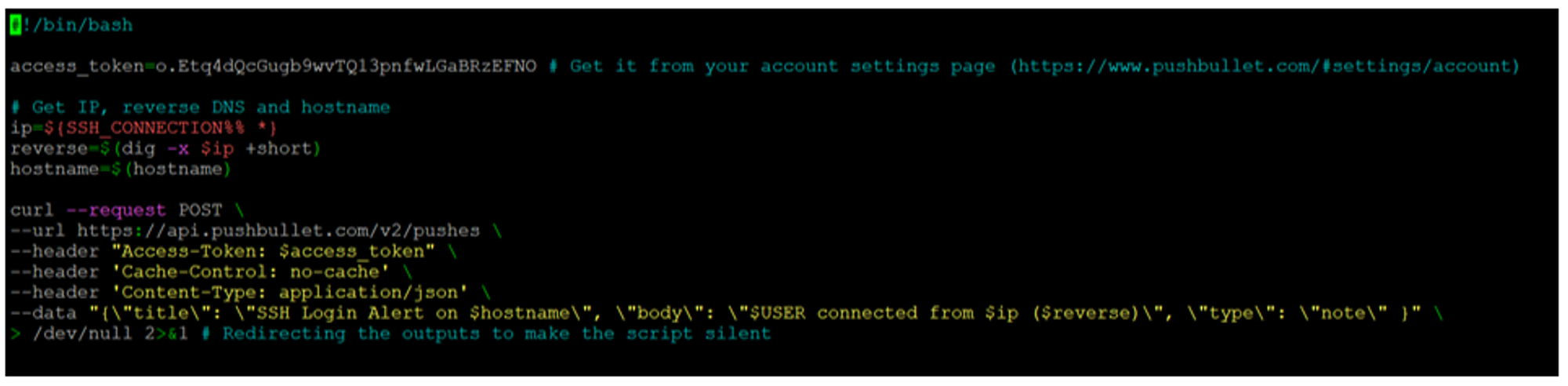
When executed, the script will use the access token to send a Pushbullet notification on the SSH connection.
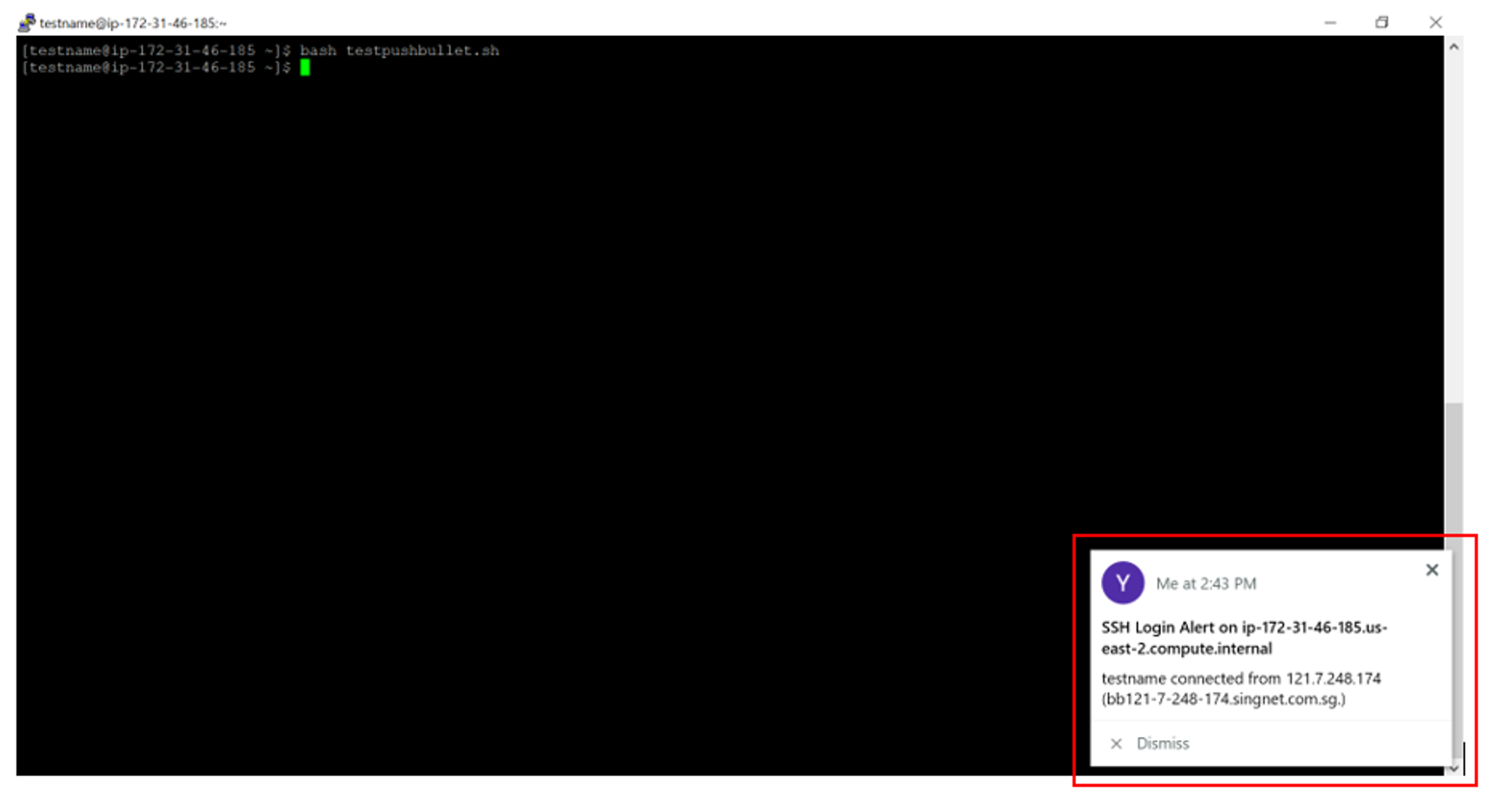
The notification will contain information pertaining to the SSH connection e.g. IP address, hostname, username. An example of the notification is shown in the screenshot below:
In order to run the script automatically whenever a SSH connection has been established, I made use of the ForceCommand method. This can be done by adding ForceCommand /usr/bin/scriptname.sh at the bottom of the file /etc/ssh/sshd_config. Next, execute the following command:
sudo chmod +x /usr/bin/scriptname.sh to make the script executable. Lastly, restart the ssh service using the following command: sudo systemctl restart sshd in order for the changes to take effect. Once done, the script will now be executed automatically whenever there is a successful SSH shell-in.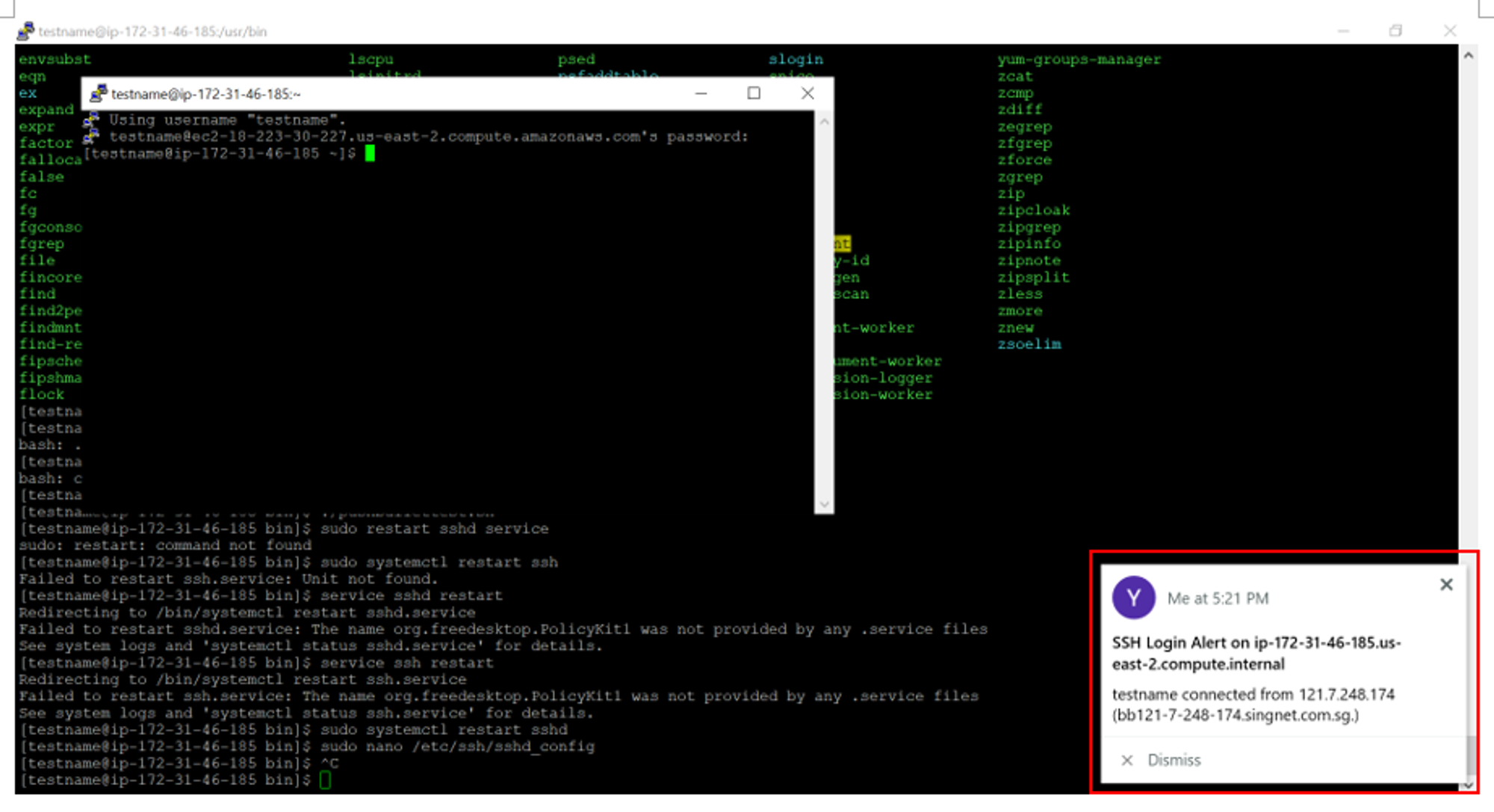
In conclusion, alert mechanisms such as Pushbullet are essential to alert users to possible SSH attacks. For example, if a user did not login via SSH and he received a SSH login notification from Pushbullet, it means that someone has successfully gained access to the user's machine through SSH. With the use of alert mechanisms, the immediate detection of attacks would allow for fast response to mitigate the damage done from the attack.